Security is nothing if not an evolving concept, and today’s most advanced security strategists are constantly looking for ways to take their expertise to the next level. This has been a welcome development, considering how dramatically our work has evolved in recent years.
Now, the technologies and techniques we have at our disposal are sometimes more complex, nuanced, and time-consuming than ever before. This article focuses on how our knowledge of security has evolved and how it continues to change to protect businesses.
Benefits of a Well-Developed Security Operation
1. Hacker-In-The-Middle (HITM) Attacks
Hacker-in-the-middle attacks are a type of attack where the hacker can intercept the data flowing between two parties by inserting himself as a third node. To do this, the hacker changes details such as IP addresses and ports, which he can do if he has access to traffic management equipment.
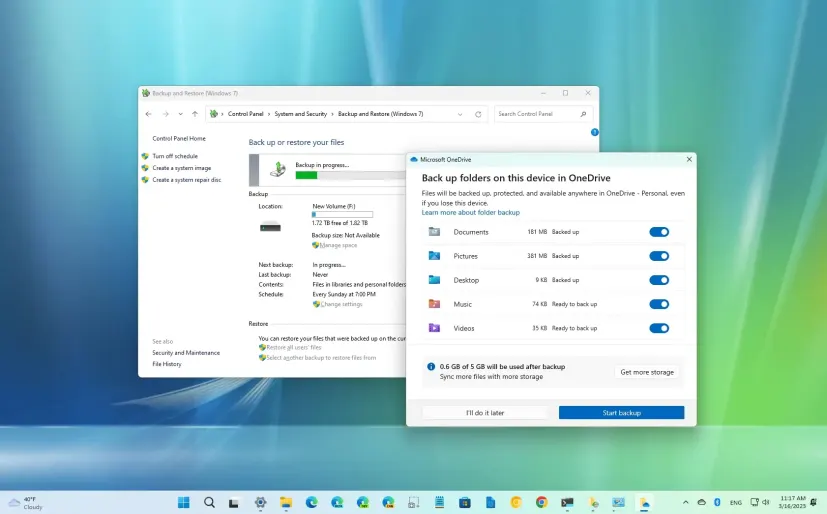
To detect HITM attacks, it is essential to have a security operations center (SOC) that monitors for potential threats 24/7. The functionality of the SOC is also crucial for identifying and flagging potential incidents in real-time.
The data collected through threat intelligence and endpoint protection solutions are used to create an environment where the SOC can respond quickly by routing traffic via different networks or using a proxy server before sending it on to its final destination.
To prevent an attack, a machine or user must be authenticated and authorized at all times. If a hacker falls under this category, the intruder will not access data that should not have been accessed.
2. Unauthorized Mobile Device Use
Mobile devices such as smartphones and tablets can be used for various tasks, but they are also vulnerable to being compromised. Hackers can install malware onto a mobile device, encouraging users to click on an infected link or download an attachment that could spread across the system via email.
Therefore, organizations need to consider this threat when planning how they will control access to data.
3. Requirement for Security Automation
SecOps also enables the automation of security processes, which greatly improves efficiency and reduces the time to respond to security incidents. Security professionals can focus more on critical tasks requiring human intervention by automating tasks and using machine-to-machine communication methods.
4. Predictive Analytics
Preventing a security incident could be as simple as turning off the lights because it is dark outside. Unfortunately, security incidents are not as easy to predict, but automated tools that monitor suspicious activity when the system is turned on could help.
A predictive analytics system may detect a significant increase in traffic coming into a certain room, for example, or that an employee appears to be carrying out unusual tasks within the building during normal working hours.
Understanding the normal pattern of behavior within the organization will make it easier to spot abnormalities and respond to them, preventing them from ever occurring.
SecOps versus DevSecOps: What’s the Difference
Both have slightly different meanings, but they are both related to security operations. In terms of how they differ, SecOp is about the people, practices, and tools used to protect an organization from external and internal threats. Its requirements include monitoring tools to detect emerging network threats and threat intelligence to recognize potential security problems in advance.
Development, security, and operations focus on the people and technology used to protect organizations; Development, security, and operations focus on developers and their tools. This is because developers need to adhere to security development practices that are more stringent than those required for security operations professionals.
Challenges
For an organization to implement a successful Security operations strategy, they must first identify where they are about their competitors.
Internal Challenges
Security operations require skilled staff, but this is not always easy in terms of the Budget and available human resources. Therefore, it is important for organizations to understand their current skill level and whether they have the right people with the necessary talents.
External Challenges
The main challenge when implementing Security operations is the human element. However, there are also challenges related to Budget and technology. Its Budget is often a fixed resource that must be deployed within the organization and can only be increased with the coordination of managers and business leaders.
In addition, security technologies like firewalls, intrusion detection systems (IDS), web application firewalls (WAF), or other solutions should be considered when planning how to implement them.
Implementation best practices
Implementing it will require a change in mindset and the willingness to learn new skills. It is therefore important for security professionals to be able to communicate effectively with employees.
For an organization to achieve its goals, it must coordinate security operations with other teams across the business. This will make it easier to implement and help ensure that security operations are aligned with business goals and objectives.
Security operations are an important part of any organization’s security strategy, but they can be easily left out due to the common misconception that it is not a necessary component. As a result, organizations could find themselves vulnerable to serious security threats, regardless of whether they are protecting valuable data or not. You can get faster and more accurate detection of both known and unknown threats by using a security analytics-powered SOC like the one offered by Micro Focus.